I want to use an SSH tunnel through AWS Systems Manager to access my private VPC resources. How can I do this?
Short description

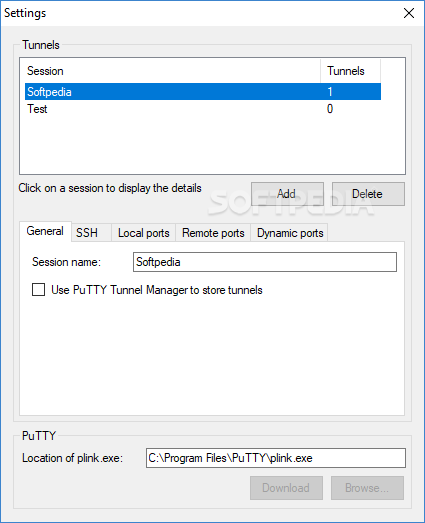
The missing tunnel manager, compatible with OpenSSH, automatic and intuitive. Don't waste your time; be productive. Contextual help provides immediate information for ssh directives. Automatic reconnect. Core Tunnel tries to restore your connections after network failure or waking up from sleep. SSH stands for Secure Shell and is the go-to network protocol for creating a secure tunnel between two devices. This tunnel is regarded as secure and private thanks to SSH’s use of strong encryption and is used as one of the primary ways of managing servers remotely. SSH Tunnel Manager. SSH Tunnel Manager lets you establish network tunnels between SSH enabled hosts. V2.2.7 downloaddownload.
Persistent SSH tunnel manager works as Windows system service. All your SSH tunnels become available immediatelly after Windows startup and will work even if no user logged in.
AWS Systems Manager Session Manager uses the Systems Manager infrastructure to create an SSH-like session with an instance. Session Manager tunnels real SSH connections, allowing you to tunnel to another resource within your virtual private cloud (VPC) directly from your local machine. A managed instance that you create acts as a bastion host, or gateway, to your AWS resources. The benefits of this configuration are:
- Increased Security: This configuration uses only one Amazon Elastic Compute Cloud (Amazon EC2) instance (the bastion host), and connects outbound port 443 to Systems Manager infrastructure. This allows you to use Session Manager without any inbound connections. The local resource must allow inbound traffic only from the instance acting as bastion host. Therefore, there is no need to open any inbound rule publicly.
- Ease of use: You can access resources in your private VPC directly from your local machine.
Note: For instructions to access your EC2 instances with a terminal or a single port forwarding using Systems Manager, see Setting up Session Manager.
Prerequisites
Enable SSH connections through Session Manager and make sure that SSH connection requirements are met.
Note: You must have the following installed to use the SSH feature:
1. AWS Systems Manager Agent (SSM Agent) v2.3.672.0 or newer.
2. Session Manager Plugin v1.1.23 or newer on your local machine.
3. AWS CLI v1.16.12 or newer on your local machine.
Resolution
To start the SSH tunnel using Session Manager, follow these steps:
Note: If you receive errors when running AWS CLI commands, make sure that you’re using the most recent version of the AWS CLI.
1. To start the SSH tunnel, run the following command:
2. To test access to the tunnel on the target port created in step 1, run the following command:
In the preceding example, 127.0.0.1 and localport translate to access targethost:destport.
Example Configurations
Scenario 1
Create a tunnel from your local machine to access a MySQL database running on an EC2 instance using the SSM host as a bastion host.
Resources used
instance1: An EC2 instance acting as a bastion host and managed by AWS Systems Manager.
Hostname = ec2-198-51-100-1.compute-1.amazonaws.com Instance id = i-0123456789abcdefa
instance2: An EC2 instance running MySQL Database on the default port 3306.
Hostname = ec2-198-51-100-2.compute-1.amazonaws.com
Instructions
1. From a local machine (for example, your laptop), run the SSH command to connect to instance1, using Session Manager-based SSH. This command establishes a tunnel to port 3306 on instance2, and presents it in your local machine on port 9090.
Note: In the preceding example, port 9090 is available on the local machine.
2. From the local machine, access the database using the available port used in step 1 (in this example, 9090).
Important: Any security groups, network access control list (network ACL), security rules, or third-party security software that exist on instance2 must allow traffic from instance1. In the preceding example, instance2 must allow port 3306 access from instance1.
Scenario 2
Create three tunnels over a single SSH connection from your local machine to:
- Connect to the SSH port in instance1
- Access a MySQL database in RDS instance
- Access a webserver in instance3
Resources used
instance1: An EC2 instance acting as a bastion host and managed by AWS Systems Manager.
Hostname = ec2-198-51-100-1.compute-1.amazonaws.com Instance id = i-0123456789abcdefa
RDS instance: A MySQL RDS instance located in a private subnet.
Hostname = DBinstanceidentifier.abcdefg12345.region.rds.amazonaws.com
instance3: An EC2 instance located in a private subnet
Hostname = ec2-198-51-100-3.compute-3.amazonaws.com
Instructions
Ssh Tunnel Manager Gui
1. Start the session with three tunnels using the SSH command.
Note: There are three separate tunnel invocations in the command.
Note: In the preceding example, ports 8080, 9090, and 9091 are available on the local machine.
2. Access SSH from the local machine to instance1. The local port 8080 tunnels to the SSH port (22) on instance1. The key-pair and username are for the instance you are tunneling to (instance1, in this example).
3. Access the database on RDS instance. The local port 9090 tunnels to port 3306 on RDS instance. You can use MySQL workbench, which allows you to access the DB server using the GUI, with 127.0.0.1 as hostname and 9090 as port. Or, run the following command in the shell command prompt:
4. From the local machine, to access the website on instance3, open the browser and navigate to the website.
Important: Any security groups, network ACL, security rules, or third-party security software that exist on RDS instance and instance3 must allow traffic from instance1. In the preceding example, instance3 must allow port 80 access from instance1.
Related information
ssh (SSH client) is a program for logging into a remote machine and for executing commands on a remote machine. It is intended to provide secure encrypted communications between two untrusted hosts over an insecure network. X11 connections, arbitrary TCP ports and UNIX-domain sockets can also be forwarded over the secure channel.
ssh connects and logs into the specified destination, which may be specified as either [user@]hostname or a URI of the form ssh://[user@]hostname[:port]. The user must prove his/her identity to the remote machine using one of several methods (see below).
If a command is specified, it is executed on the remote host instead of a login shell.
The options are as follows:
-4ssh to use IPv4 addresses only. -6ssh to use IPv6 addresses only. -AAgent forwarding should be enabled with caution. Users with the ability to bypass file permissions on the remote host (for the agent's UNIX-domain socket) can access the local agent through the forwarded connection. An attacker cannot obtain key material from the agent, however they can perform operations on the keys that enable them to authenticate using the identities loaded into the agent. A safer alternative may be to use a jump host (see -J).
-a-Bbind_interface-bbind_address-CCompression option. -ccipher_specCiphers keyword in ssh_config(5) for more information. -D [bind_address:]portssh will act as a SOCKS server. Only root can forward privileged ports. Dynamic port forwardings can also be specified in the configuration file. IPv6 addresses can be specified by enclosing the address in square brackets. Only the superuser can forward privileged ports. By default, the local port is bound in accordance with the GatewayPorts setting. However, an explicit bind_address may be used to bind the connection to a specific address. The bind_address of “localhost” indicates that the listening port be bound for local use only, while an empty address or ‘*’ indicates that the port should be available from all interfaces.
-Elog_file-eescape_char~’). The escape character is only recognized at the beginning of a line. The escape character followed by a dot (‘.’) closes the connection; followed by control-Z suspends the connection; and followed by itself sends the escape character once. Setting the character to “none” disables any escapes and makes the session fully transparent. -Fconfigfile-fssh to go to background just before command execution. This is useful if ssh is going to ask for passwords or passphrases, but the user wants it in the background. This implies -n. The recommended way to start X11 programs at a remote site is with something like ssh -f host xterm. If the ExitOnForwardFailure configuration option is set to “yes”, then a client started with -f will wait for all remote port forwards to be successfully established before placing itself in the background.
-GSsh Tunnel Manager Google Code
ssh to print its configuration after evaluating Host and Match blocks and exit. -g-Ipkcs11ssh should use to communicate with a PKCS#11 token providing keys for user authentication. -iidentity_file-i options (and multiple identities specified in configuration files). If no certificates have been explicitly specified by the CertificateFile directive, ssh will also try to load certificate information from the filename obtained by appending -cert.pub to identity filenames. -Jdestinationssh connection to the jump host described by destination and then establishing a TCP forwarding to the ultimate destination from there. Multiple jump hops may be specified separated by comma characters. This is a shortcut to specify a ProxyJump configuration directive. Note that configuration directives supplied on the command-line generally apply to the destination host and not any specified jump hosts. Use ~/.ssh/config to specify configuration for jump hosts. -K-k-L [bind_address:]port:host:hostport-L [bind_address:]port:remote_socket-Llocal_socket:host:hostport-Llocal_socket:remote_socketPort forwardings can also be specified in the configuration file. Only the superuser can forward privileged ports. IPv6 addresses can be specified by enclosing the address in square brackets.
Ssh Tunnel Manager Windows
By default, the local port is bound in accordance with the GatewayPorts setting. However, an explicit bind_address may be used to bind the connection to a specific address. The bind_address of “localhost” indicates that the listening port be bound for local use only, while an empty address or ‘*’ indicates that the port should be available from all interfaces.
-llogin_name-Mssh client into “master” mode for connection sharing. Multiple -M options places ssh into “master” mode but with confirmation required using ssh-askpass(1) before each operation that changes the multiplexing state (e.g. opening a new session). Refer to the description of ControlMaster in ssh_config(5) for details. -mmac_specMACs keyword for more information. -N-nssh is run in the background. A common trick is to use this to run X11 programs on a remote machine. For example, ssh -n shadows.cs.hut.fi emacs & will start an emacs on shadows.cs.hut.fi, and the X11 connection will be automatically forwarded over an encrypted channel. The ssh program will be put in the background. (This does not work if ssh needs to ask for a password or passphrase; see also the -f option.) -Octl_cmd-O option is specified, the ctl_cmd argument is interpreted and passed to the master process. Valid commands are: “check” (check that the master process is running), “forward” (request forwardings without command execution), “cancel” (cancel forwardings), “exit” (request the master to exit), and “stop” (request the master to stop accepting further multiplexing requests). -ooption- AddKeysToAgent
- AddressFamily
- BatchMode
- BindAddress
- CanonicalDomains
- CanonicalizeFallbackLocal
- CanonicalizeHostname
- CanonicalizeMaxDots
- CanonicalizePermittedCNAMEs
- CASignatureAlgorithms
- CertificateFile
- ChallengeResponseAuthentication
- CheckHostIP
- Ciphers
- ClearAllForwardings
- Compression
- ConnectionAttempts
- ConnectTimeout
- ControlMaster
- ControlPath
- ControlPersist
- DynamicForward
- EscapeChar
- ExitOnForwardFailure
- FingerprintHash
- ForwardAgent
- ForwardX11
- ForwardX11Timeout
- ForwardX11Trusted
- GatewayPorts
- GlobalKnownHostsFile
- GSSAPIAuthentication
- GSSAPIDelegateCredentials
- HashKnownHosts
- Host
- HostbasedAcceptedAlgorithms
- HostbasedAuthentication
- HostKeyAlgorithms
- HostKeyAlias
- Hostname
- IdentitiesOnly
- IdentityAgent
- IdentityFile
- IPQoS
- KbdInteractiveAuthentication
- KbdInteractiveDevices
- KexAlgorithms
- KnownHostsCommand
- LocalCommand
- LocalForward
- LogLevel
- MACs
- Match
- NoHostAuthenticationForLocalhost
- NumberOfPasswordPrompts
- PasswordAuthentication
- PermitLocalCommand
- PermitRemoteOpen
- PKCS11Provider
- Port
- PreferredAuthentications
- ProxyCommand
- ProxyJump
- ProxyUseFdpass
- PubkeyAcceptedAlgorithms
- PubkeyAuthentication
- RekeyLimit
- RemoteCommand
- RemoteForward
- RequestTTY
- SendEnv
- ServerAliveInterval
- ServerAliveCountMax
- SetEnv
- StreamLocalBindMask
- StreamLocalBindUnlink
- StrictHostKeyChecking
- TCPKeepAlive
- Tunnel
- TunnelDevice
- UpdateHostKeys
- User
- UserKnownHostsFile
- VerifyHostKeyDNS
- VisualHostKey
- XAuthLocation
-pport-Qquery_optionssh for the algorithms supported for the specified version 2. The available features are: cipher (supported symmetric ciphers), cipher-auth (supported symmetric ciphers that support authenticated encryption), help (supported query terms for use with the -Q flag), mac (supported message integrity codes), kex (key exchange algorithms), key (key types), key-cert (certificate key types), key-plain (non-certificate key types), key-sig (all key types and signature algorithms), protocol-version (supported SSH protocol versions), and sig (supported signature algorithms). Alternatively, any keyword from ssh_config(5) or sshd_config(5) that takes an algorithm list may be used as an alias for the corresponding query_option. -q-R [bind_address:]port:host:hostport-R [bind_address:]port:local_socket-Rremote_socket:host:hostport-Rremote_socket:local_socket-R [bind_address:]portThis works by allocating a socket to listen to either a TCP port or to a Unix socket on the remote side. Whenever a connection is made to this port or Unix socket, the connection is forwarded over the secure channel, and a connection is made from the local machine to either an explicit destination specified by host port hostport, or local_socket, or, if no explicit destination was specified, ssh will act as a SOCKS 4/5 proxy and forward connections to the destinations requested by the remote SOCKS client.
Port forwardings can also be specified in the configuration file. Privileged ports can be forwarded only when logging in as root on the remote machine. IPv6 addresses can be specified by enclosing the address in square brackets.
By default, TCP listening sockets on the server will be bound to the loopback interface only. This may be overridden by specifying a bind_address. An empty bind_address, or the address ‘*’, indicates that the remote socket should listen on all interfaces. Specifying a remote bind_address will only succeed if the server's GatewayPorts option is enabled (see sshd_config(5)).
If the port argument is ‘0’, the listen port will be dynamically allocated on the server and reported to the client at run time. When used together with -O forward the allocated port will be printed to the standard output.
-Sctl_pathControlPath and ControlMaster in ssh_config(5) for details. -s-T-t-t options force tty allocation, even if ssh has no local tty. -V-vssh to print debugging messages about its progress. This is helpful in debugging connection, authentication, and configuration problems. Multiple -v options increase the verbosity. The maximum is 3. -Whost:port-N, -T, ExitOnForwardFailure and ClearAllForwardings, though these can be overridden in the configuration file or using -o command line options. -wlocal_tun[:remote_tun]
The devices may be specified by numerical ID or the keyword “any”, which uses the next available tunnel device. If remote_tun is not specified, it defaults to “any”. See also the Tunnel and TunnelDevice directives in ssh_config(5).
If the Tunnel directive is unset, it will be set to the default tunnel mode, which is “point-to-point”. If a different Tunnel forwarding mode it desired, then it should be specified before -w.
-XX11 forwarding should be enabled with caution. Users with the ability to bypass file permissions on the remote host (for the user's X authorization database) can access the local X11 display through the forwarded connection. An attacker may then be able to perform activities such as keystroke monitoring.
For this reason, X11 forwarding is subjected to X11 SECURITY extension restrictions by default. Please refer to the ssh-Y option and the ForwardX11Trusted directive in ssh_config(5) for more information.
-x-Y-yssh may additionally obtain configuration data from a per-user configuration file and a system-wide configuration file. The file format and configuration options are described in ssh_config(5).
